Why Privileged Access Management Is the Most Underinvested Control in Government Environments
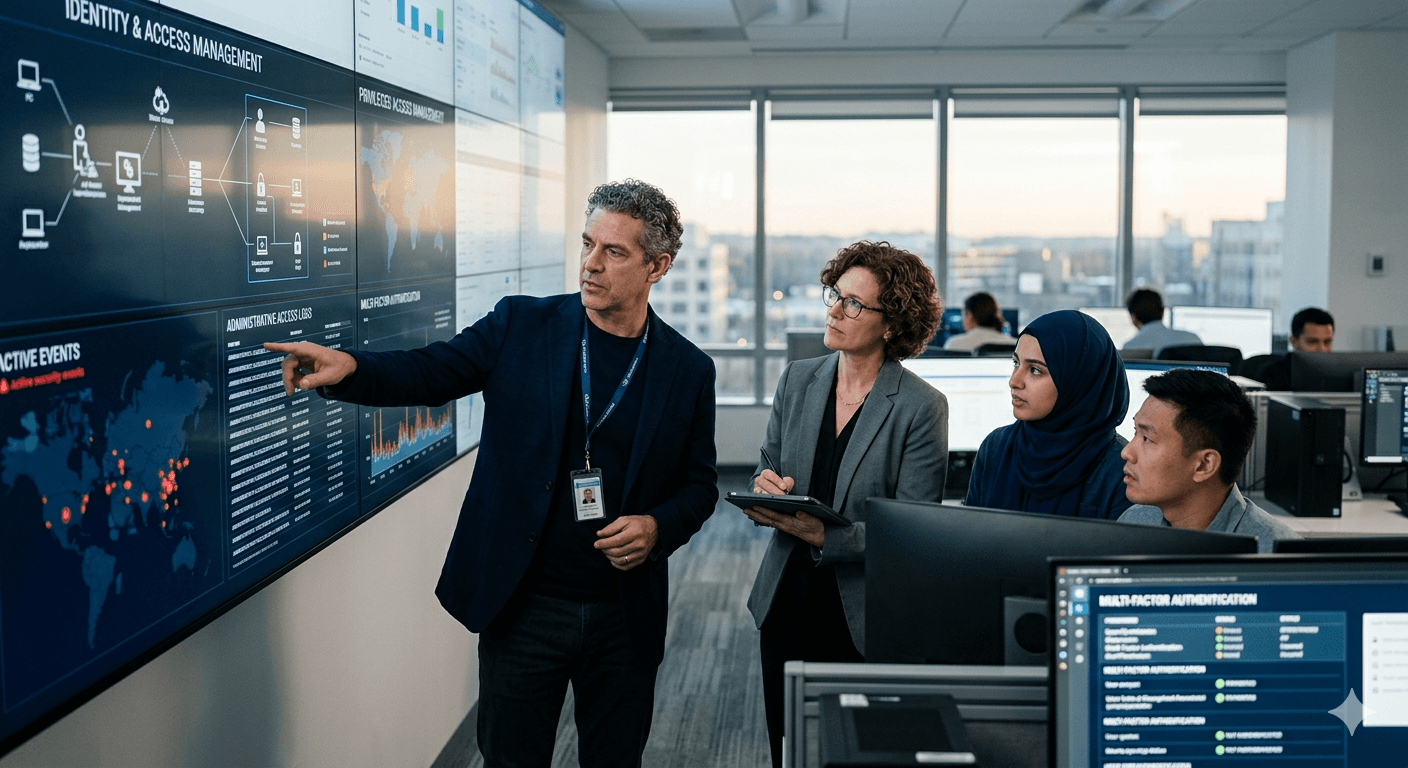
Most agencies have MFA in place. Far fewer have mature PAM programs controlling what privileged accounts can actually do once authenticated. Here’s why that gap is one of the most exploited weaknesses in federal IT environments, and what a modern PAM deployment actually looks like in practice.
Key takeaways
- Why MFA coverage doesn’t automatically protect privileged actions
- What PAM should control after authentication
- How to sequence PAM for real operational adoption
Most government environments have improved authentication controls over the last few years, but the control gap rarely gets addressed at the privileged layer. Once a privileged account is authenticated, what happens next determines whether MFA meaningfully reduces risk.
A mature PAM program goes beyond 'password management.' It governs privilege elevation, enforces strong credential handling, and controls what privileged identities can actually perform during active sessions. In practice, that means vaulting, just-in-time access, session monitoring, and access reviews that keep privilege aligned to operational needs.
If you’re planning PAM, the most common failure mode is sequencing: treating PAM as a late-stage add-on instead of building it around the privileged workflows your teams depend on. When implemented correctly, PAM reduces blast radius, improves traceability, and strengthens audit-ready evidence.