Cybersecurity Intelligence From the People Doing the Work.
Practical threat intelligence, compliance guidance, and operational security insights from AyonGate's team of certified cybersecurity professionals, written for the people responsible for protecting critical missions, not for search engine rankings.

Zero Trust Is Not a Product. Here’s What It Actually Takes to Implement It.
Every vendor claims their solution delivers Zero Trust. The reality is that Zero Trust is an architecture, a philosophy, and a journey; not a checkbox or a single platform purchase. Most organizations pursuing Zero Trust mandates under Executive Order 14028 are starting in the wrong place: buying technology before establishing the identity foundation that makes everything else work. This guide breaks down what a genuine Zero Trust implementation actually looks like across all five CISA pillars and the sequencing mistakes that cause most programs to stall before they deliver results.
Read the Full Article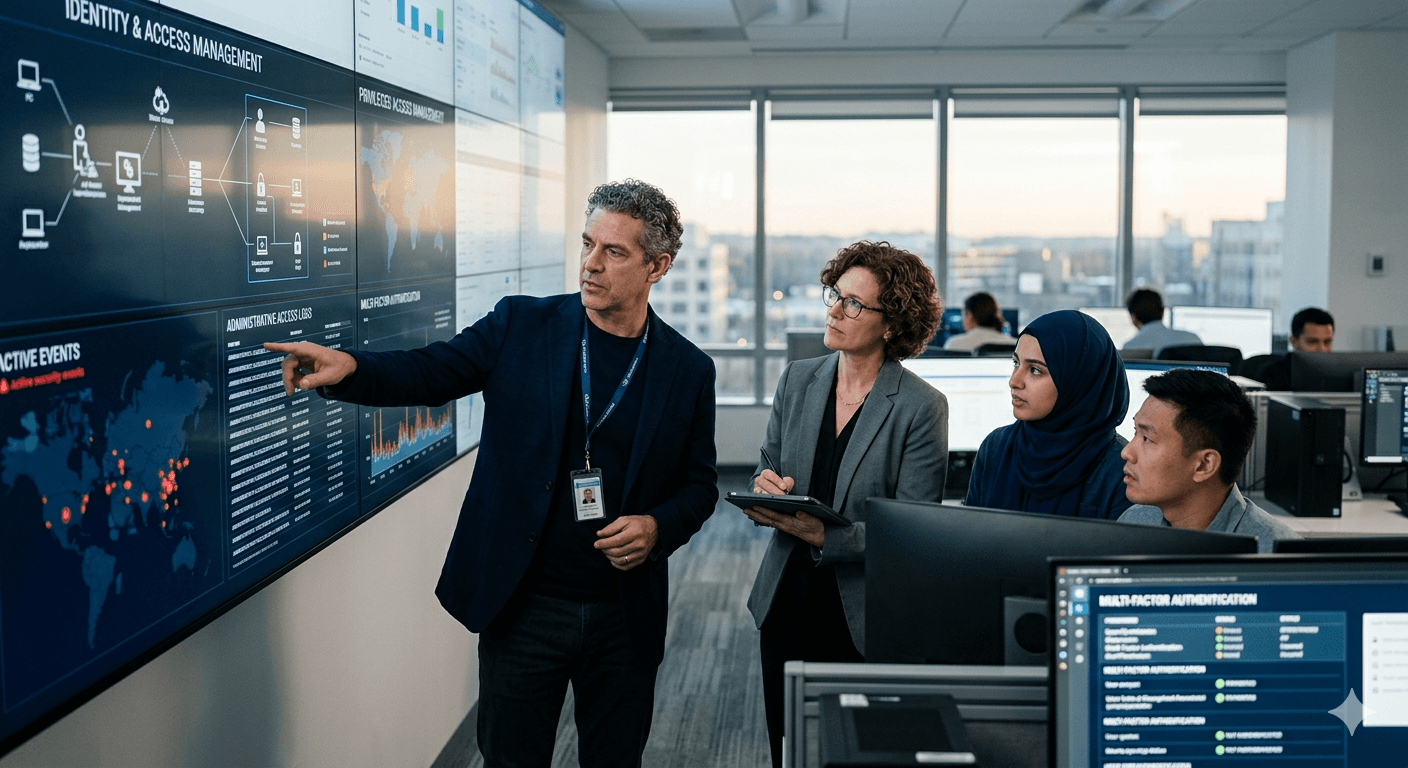
Why Privileged Access Management Is the Most Underinvested Control in Government Environments
Most agencies have MFA in place. Far fewer have mature PAM programs controlling what privileged accounts can actually do once authenticated. Here’s why that gap is one of the most exploited weaknesses in federal IT environments, and what a modern PAM deployment actually looks like in practice.
Read More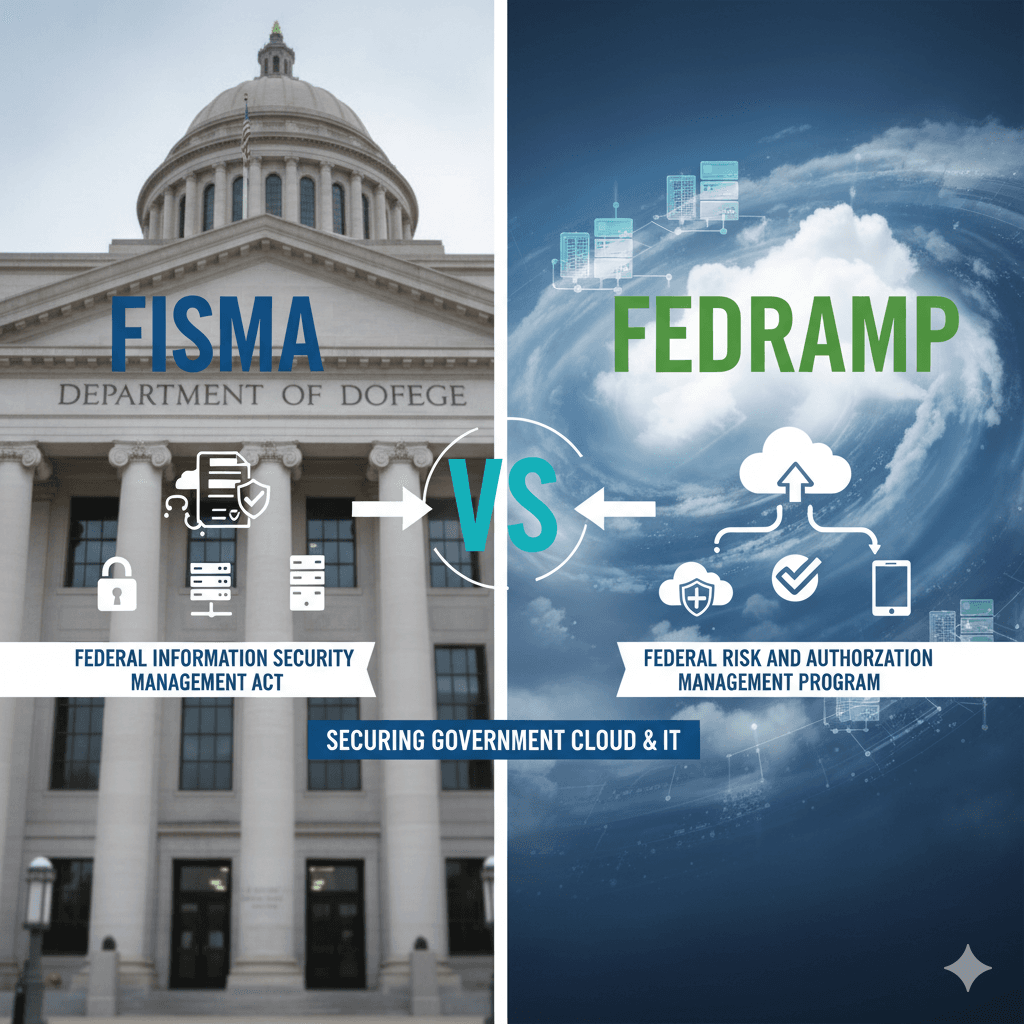
FISMA vs FedRAMP: Understanding the Difference and Why Both Matter to Your Agency
FISMA and FedRAMP are frequently confused, often conflated, and critically important to get right. This guide breaks down what each framework requires, who it applies to, how they interact, and what agencies and cloud service providers need to do to stay compliant and operationally secure.
Read More
The SIEM Trap: Why Most Government SIEMs Are Generating Noise Instead of Catching Threats
A SIEM that generates hundreds of alerts a day and catches nothing real is not a security tool; it is a liability. This post examines the most common SIEM implementation failures in government environments and the detection engineering practices that separate SIEMs that actually work from ones that just look like they do.
Read More
The First 60 Minutes of a Breach: What You Do Right Now Determines Everything
Incident response is not something you figure out after a breach starts. The decisions made in the first hour (what to isolate, what to preserve, who to call, what not to do) determine whether an incident is a contained disruption or a full operational crisis. Here is exactly what those first 60 minutes should look like.
Read More
The Shared Responsibility Model: What Your Cloud Provider Secures and What Is Entirely Your Problem
The single most dangerous misunderstanding in cloud security is the belief that moving to the cloud means your provider handles security. They handle part of it. Everything above the infrastructure layer (your data, your configurations, your access controls, your workloads) is yours. Here is exactly where the line sits across AWS, Azure, and Google Cloud.
Read More
Why Your Compliance Program Is Passing Audits and Getting You Breached at the Same Time
Compliance and security are not the same thing. An organization can satisfy every NIST 800-53 control on paper while remaining operationally vulnerable to attacks that those controls were designed to prevent. This post examines the gap between compliance posture and actual security posture, and what it takes to close it.
Read More
Executive Order 14028: What Federal Agencies Are Actually Required to Do and Where Most Are Falling Short
Executive Order 14028 on Improving the Nation’s Cybersecurity created specific, binding requirements for federal agencies: Zero Trust architecture, SBOM requirements, cloud security standards, and incident reporting mandates. Two years in, compliance is uneven and many agencies are further behind than they realize. Here is what is actually required and where the gaps tend to be.
Read More
What a Penetration Test Actually Tells You, and What It Does Not
Penetration testing is one of the most misunderstood services in cybersecurity. Organizations often treat a clean pentest result as evidence of strong security. It is not. Here is what a penetration test actually measures, what it cannot tell you, and how to use pentest findings to drive meaningful security improvement rather than check a compliance box.
Read More
IT/OT Convergence: Why Securing Critical Infrastructure Is Fundamentally Different From Enterprise Security
Cybersecurity professionals trained in enterprise IT environments often make dangerous assumptions when they move into critical infrastructure contexts, because the priorities are different, the consequences of failure are different, and many standard security practices are simply not applicable. Here is what every cybersecurity professional needs to understand before working in an OT environment.
Read MoreGet AyonGate Insights Delivered to Your Inbox.
New articles, threat intelligence updates, and compliance guidance, delivered monthly. No spam, no marketing fluff. Just useful cybersecurity content from practitioners who do this work every day.