Defend What Can’t
Afford to Fail.
Advanced Cybersecurity for Government Agencies and Critical Infrastructure.
AyonGate Technologies partners with federal agencies, state and local governments, and critical infrastructure operators to build resilient, compliance-ready security programs. From identity management to threat detection, we protect your mission before, during, and after an attack.

The Threats Are Real.
The Stakes Are Higher Than Ever.
Government agencies and critical infrastructure operators are among the most targeted organizations in the world. Ransomware, supply chain attacks, insider threats, and advanced persistent threats don’t wait for budget cycles or procurement timelines; they move fast, strike hard, and exploit every gap in your defenses.
Most organizations aren’t breached because they lacked technology. They’re breached because the right expertise wasn’t in place at the right time.
Legacy systems, understaffed security teams, misaligned compliance programs, and reactive postures leave mission-critical operations dangerously exposed. The question isn’t whether your environment will be targeted; it’s whether you’ll be ready when it is.
Expanding Attack Surface
Hybrid cloud environments, remote access points, and third-party integrations have created more entry points than most teams can effectively monitor or defend.
Compliance Without Security
Checking compliance boxes doesn’t mean you’re secure. Many agencies meet regulatory requirements on paper while remaining operationally vulnerable to real-world threats.
Reactive Security Posture
Waiting until an incident occurs to act is no longer an option. By the time a breach is detected, the damage, operational, financial, and reputational, is already done.
This is exactly why AyonGate Technologies exists.
See How We Solve This →Built by a Practitioner. Trusted by Mission-Critical Organizations.
AyonGate Technologies was founded in 2025 by Maximus Banla, a CISSP-certified cybersecurity professional with over a decade of hands-on experience protecting enterprise and government-aligned environments. AyonGate wasn’t built in a boardroom; it was built in the trenches of Security Operations Centers, incident response engagements, and identity management deployments where the stakes were real and the margin for error was zero.
We created AyonGate because we saw a gap in the market. Government agencies and critical infrastructure operators needed more than vendors selling software licenses or generalist consultants recycling frameworks. They needed a trusted partner: one with deep technical expertise, genuine federal alignment, and the operational experience to deliver security programs that actually work under pressure.
Today, AyonGate operates as a founder-led, boutique cybersecurity firm serving clients nationwide. Every engagement is personally overseen by certified leadership. Every recommendation is grounded in real-world experience. And every solution is built around your mission, not a generic template.
We don’t just advise. We defend.
Comprehensive Cybersecurity Services
Built for High-Stakes Environments.
From identity and access management to zero trust architecture, AyonGate delivers end-to-end security capabilities aligned to federal frameworks and mission requirements.
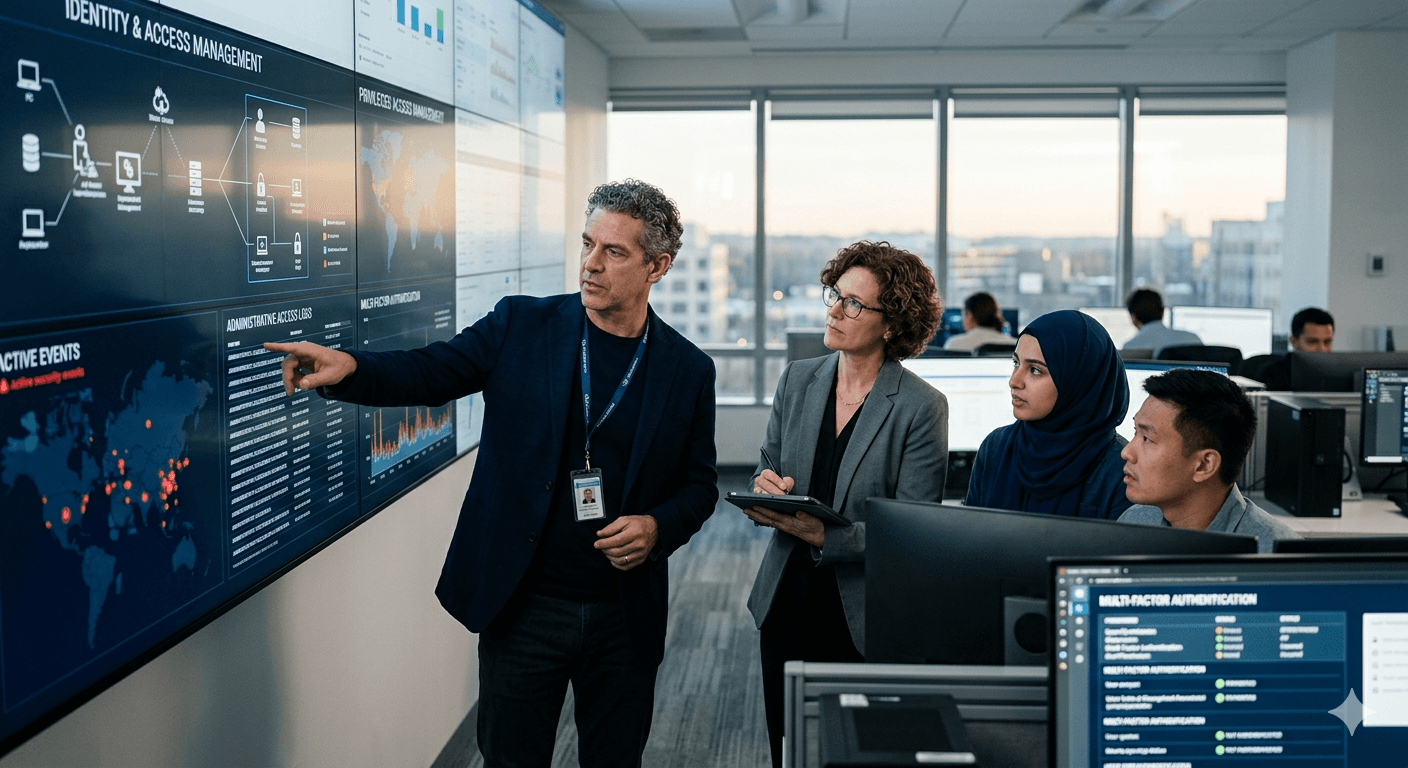
Identity & Access Management
We design and implement robust IAM programs using Okta, SSO, MFA, and PAM solutions that ensure only the right people access the right systems, at the right time.
Learn More →Cloud Security
We secure hybrid and multi-cloud environments with architecture reviews, configuration hardening, continuous monitoring, and cloud-native security controls built for resilience.
Learn More →Threat Detection & SIEM
Our analysts deploy and manage SIEM platforms with advanced KQL-based threat hunting, custom detection rules, and real-time alerting to identify threats before they escalate.
Learn More →Incident Response
When a breach occurs, speed is everything. AyonGate provides rapid incident response, containment, investigation, eradication, and recovery, to minimize damage and restore operations fast.
Learn More →Zero Trust Architecture
We design and implement Zero Trust frameworks aligned to CISA guidelines, eliminating implicit trust across your network and enforcing strict identity verification at every access point.
Learn More →Penetration Testing
Our offensive security team conducts thorough penetration tests across networks, applications, and infrastructure, delivering actionable findings that prioritize your highest-risk exposures.
Learn More →GRC Program Development
We build and mature Governance, Risk, and Compliance programs aligned to NIST, FISMA, and FedRAMP, turning compliance requirements into operational security strengths.
Learn More →DevSecOps & Secure SDLC
We embed security into your development pipeline from the ground up, integrating automated security testing, code reviews, and vulnerability management into every stage of your software lifecycle.
Learn More →Endpoint Detection & Response
We deploy and manage EDR and XDR solutions that provide deep visibility into endpoint activity, enabling rapid detection, investigation, and response to threats across your entire environment.
Learn More →The Difference Between a Vendor
and a Trusted Security Partner.
Anyone can sell you a security tool. Very few can architect, implement, and operationalize a security program that holds up under real-world pressure. Here’s what sets AyonGate apart.
CISSP-Certified Leadership
Every engagement at AyonGate is led by CISSP-certified professionals. You’re not getting a junior consultant reading from a playbook, you’re getting a seasoned practitioner who has operated in high-stakes environments and knows exactly what it takes to protect them.
10+ Years of Hands-On Experience
Our expertise wasn’t built in a classroom. It was forged through more than a decade of real-world security operations, incident response engagements, and identity management deployments across enterprise and government environments.
Deep Federal Framework Alignment
We don’t just know NIST, FISMA, and FedRAMP, we operationalize them. Our team translates complex federal compliance requirements into practical, enforceable security controls that protect your mission and satisfy your auditors.
Founder-Led, Boutique Firm
As a founder-led boutique firm, AyonGate offers something larger contractors simply can’t, direct access to senior expertise on every single engagement. No bait-and-switch. No hand-offs to inexperienced staff.
Rapid Response Capabilities
Cyber threats don’t wait for business hours. AyonGate is built for speed, whether it’s responding to an active incident, closing a critical vulnerability, or standing up emergency security controls.
Strategic, Long-Term Partnership
We don’t disappear after implementation. AyonGate operates as your long-term cybersecurity partner, continuously advising, adapting, and strengthening your security posture as threats evolve.
A Proven Methodology. Designed for
Mission-Critical Environments.
Every AyonGate engagement follows a structured, repeatable process built to deliver measurable security outcomes, not just reports and recommendations that gather dust.
Discovery & Scoping
We begin every engagement with a deep-dive discovery session to understand your environment, mission requirements, existing security controls, and the specific threats most relevant to your organization.
Assessment & Gap Analysis
Our team conducts a thorough technical and compliance assessment of your current security posture, identifying vulnerabilities, misconfigurations, compliance gaps, and high-risk exposures.
Strategy & Roadmap
Based on assessment findings, we develop a prioritized security roadmap tailored to your mission, budget, and risk tolerance. Every recommendation is practical, actionable, and sequenced for impact.
Implementation & Hardening
AyonGate’s engineers roll up their sleeves and implement the solutions, deploying controls, hardening configurations, integrating platforms, and validating every safeguard.
Continuous Monitoring
After implementation, AyonGate provides ongoing monitoring, threat hunting, and program optimization to ensure your defenses stay ahead of an evolving threat landscape.
From first conversation to continuous defense, AyonGate is with you at every step.
No commitment. No pressure. Just clarity on where you stand and what to do next.
Protecting the Organizations That
Keep the Nation Running.
AyonGate Technologies delivers mission-aligned cybersecurity to the sectors where security failures carry the heaviest consequences.
Federal Government
We support federal agencies with security programs built around NIST, FISMA, and FedRAMP requirements. From authorization support to continuous monitoring, we protect the systems that drive national operations and public trust.
Learn More →State & Local Government
State and municipal agencies face the same sophisticated threats as federal entities, often with fewer resources. AyonGate delivers enterprise-grade cybersecurity scaled to the unique budget and compliance realities of state and local government.
Learn More →Critical Infrastructure
Energy grids, water systems, transportation networks, and communications infrastructure are prime targets for nation-state and criminal actors. We protect operational technology and IT environments that communities depend on every day.
Learn More →Defense & Intelligence
We support defense contractors and intelligence-adjacent organizations with security programs aligned to CMMC, RMF, and DoD cybersecurity requirements, ensuring mission readiness and supply chain integrity.
Learn More →Healthcare & Public Health
Healthcare organizations managing sensitive patient data and life-critical systems face relentless cyber threats. AyonGate delivers HIPAA-aligned security controls, incident response readiness, and resilient infrastructure protection.
Learn More →Financial Services & Fintech
Financial institutions require airtight security across transactions, data, and regulatory compliance. We deliver identity management, threat detection, and compliance programs that protect assets and maintain customer confidence.
Learn More →Don’t see your sector? We work across industries wherever security and compliance are mission-critical. Get in touch →
We Speak the Language of
Federal Compliance.
Every AyonGate engagement is grounded in the frameworks and standards that govern security in government and critical infrastructure environments. We don’t just recommend compliance; we engineer it.
The foundation of our security program design and risk management approach.
We align security controls and documentation to meet full FISMA compliance requirements.
We support cloud service providers and agencies navigating FedRAMP authorization pathways.
We prepare defense contractors for CMMC assessments across all maturity levels.
We guide organizations through the full NIST RMF process, from categorization to authorization.
“Compliance is the floor, not the ceiling. We build security programs that satisfy regulators and actually protect your mission.”
Maximus Banla, CISSP, Founder, AyonGate Technologies
Trusted by the Organizations That Can’t
Afford to Get Security Wrong.
Don’t take our word for it. Here’s what the people who work with us have to say.
“AyonGate brought a level of technical depth and federal framework expertise that we hadn’t seen from other vendors. They didn’t just deliver a compliance report, they rebuilt our entire identity management program from the ground up and made us measurably more secure.”
“When we experienced a suspected breach, AyonGate was engaged within hours. Their incident response team was methodical, calm, and thorough. They contained the threat, identified the root cause, and had us back to full operations faster than we thought possible. I can’t recommend them highly enough.”
“We needed a partner who understood both the technical and compliance sides of cybersecurity for a DoD-adjacent engagement. AyonGate delivered on both fronts. Their CMMC preparation support was thorough, practical, and exactly what our team needed to get assessment-ready with confidence.”
Your Mission Deserves More Than
a Generic Security Vendor.
AyonGate Technologies is ready to assess your environment, align your security program to federal requirements, and build the defenses your organization needs to operate with confidence. Whether you’re starting from scratch or maturing an existing program , we’re the partner built for this work.
No commitment required. We’ll assess your needs and recommend the right path forward.
Cybersecurity Intelligence From the Field.
Practical insights, threat intelligence, and compliance guidance from AyonGate’s team of certified cybersecurity professionals , written for the people responsible for protecting critical missions.
Why Privileged Access Management Is the Most Underinvested Control in Government Environments
Most agencies have MFA in place. Far fewer have mature PAM programs controlling what privileged accounts can actually do once authenticated. Here’s why that gap is one of the most exploited weaknesses in federal IT environments, and what a modern PAM deployment actually looks like in practice.
Read More →
Zero Trust Is Not a Product. Here’s What It Actually Takes to Implement It.
Every vendor claims their solution delivers Zero Trust. The reality is that Zero Trust is an architecture, a philosophy, and a journey; not a checkbox or a single platform purchase. Most organizations pursuing Zero Trust mandates under Executive Order 14028 are starting in the wrong place: buying technology before establishing the identity foundation that makes everything else work. This guide breaks down what a genuine Zero Trust implementation actually looks like across all five CISA pillars and the sequencing mistakes that cause most programs to stall before they deliver results.
Read More →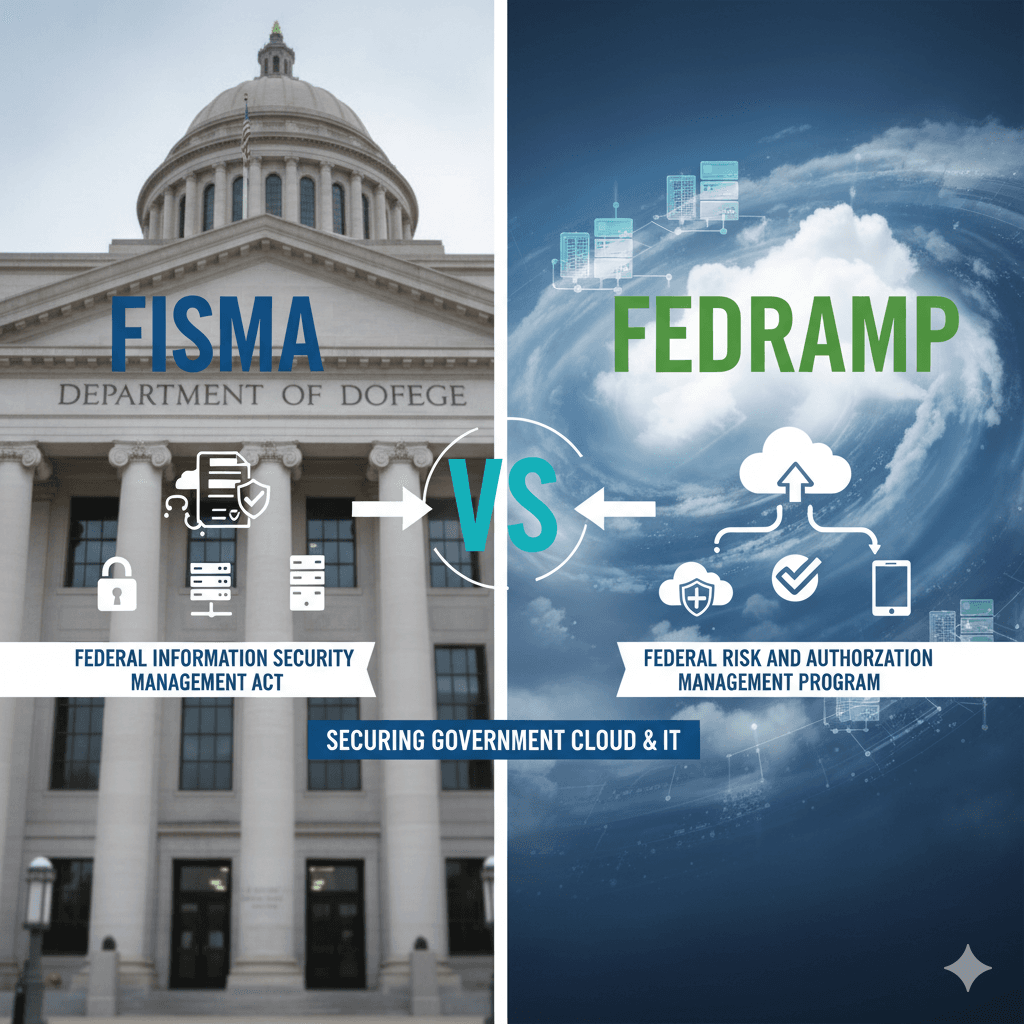
FISMA vs FedRAMP: Understanding the Difference and Why Both Matter to Your Agency
FISMA and FedRAMP are frequently confused, often conflated, and critically important to get right. This guide breaks down what each framework requires, who it applies to, how they interact, and what agencies and cloud service providers need to do to stay compliant and operationally secure.
Read More →Let’s Secure Your Mission.
Whether you’re looking to assess your current security posture, build a compliance program from the ground up, or respond to an active threat, AyonGate is ready to help. Reach out today and let’s start the conversation.
- contracts@ayongate.com
- (469) 531-6698
- Forney, Texas, Serving Clients Nationwide
- Response within 1 business day guaranteed